All you need to know about phone spoofing: what is it and how to protect yourself from the growing scams
Knowing the meaning of phone spoofing is nowadays increasingly important to avoid falling for the scams of malicious attackers, who are constantly ready to steal personal data and money via technological tools.
Fraud, unfortunately, is now the order of the day, and phones make things much easier for those who try to carry out such frauds. Phone spoofing falls right into this domain, so it’s crucial to clearly understand not only what it means, but above all how to protect yourself from such schemes and how to avoid running into them.
The meaning of telephone spoofing: what it is and types
Literally, the meaning of spoofing is connected to that of deception, cheating. With this type of attack, attackers impersonate another entity by falsifying data in order to gain an illegitimate advantage. This manipulation is based on the ability to deceive systems and users who are led (wrongly) to believe that they are communicating with a trusted source.
It is a technique that is widely used in more general phishing attacks, the ultimate goal of which is to obtain personal information, such as passwords, credit card numbers or financial details.
To really understand the meaning of spoofing, however, a distinction must be made between the different types of attacks possible. In some cases, victims may receive classic messages on their phones in which the identity of the sender is concealed in order to appear legitimate (SMS spoofing). However, there is not only message spoofing, but also voice spoofing. Malicious attackers can in fact also change phone numbers when making calls to users.
Changing the sender’s numbers and name, by the way, is not such a difficult practice. There are even providers who offer this type of service because, basically, it is not considered illegal. It is only so when it is used to defraud users. Take for instance all those companies that need to send large-scale service messages to their customers and need to hide the sender’s number. In this case, the practice appears perfectly legitimate, whereas the meaning of spoofing changes, taking on a negative connotation when the process is generated to carry out malicious actions and scams.
Then there is also e-mail spoofing, which, as the name suggests, takes place by sending e-mails. Also not to be forgotten is IP spoofing, with which fraudsters conceal the identity of a server by making the IP address of a host seemingly legitimate, or even DNS server spoofing, in which the compromise of the DNS (Domain Name Service) server results in a redirection to a malicious site. ARP spoofing must also necessarily be taken into account in order to protect oneself: in this case, forged ARP (Address Resolution Protocol) messages are sent by fraudsters.
Regardless of the type of approach adopted, all the various forms of spoofing share a fundamental element: they use trust as leverage to obtain or alter sensitive data, commit financial fraud, circumvent network access control mechanisms, and spread malicious software through malicious links and attachments.
How to protect yourself?
Identifying spoofing attacks has become increasingly difficult today and this is because, as already mentioned, falsifying the identity of senders is anything but difficult. This means that everyone should adopt sound and careful security practices.
First of all, you should only visit official and notoriously secure sites (with HTTPS protocol). Then you should think carefully about every communication you receive (on any kind of channel), even when the sender seems absolutely trustworthy.
You should then avoid entering your personal data too confidently and lightly without first having investigated the sender who is requesting that action, and you should obviously carefully analyse all links and attachments contained in received communications. A simple click on them, in fact, could have important repercussions for you.
The use of strong and robust passwords is also highly recommended. You should avoid using common names that can be linked to you, or easily identifiable dates of birth, and construct highly customised keys that are difficult to find.
Keeping your attention high, therefore, is crucial, but it is not the only thing you can do to protect yourself against spoofing. You could, for instance, decide to use a VPN to make fraud attempts more difficult (hackers would find it difficult to decipher the data of users who have encrypted their traffic). Or you could evaluate services such as blocking cookies, offered for instance by NordVPN’s Threat Protection. You could also use classic antivirus software, which is able to identify attack attempts, and firewalls that can detect addresses outside the local network.
As already stated at the beginning of this article, knowing the meaning of spoofing is more important than ever, as is keeping alert to the countless fraud attempts to which we are unfortunately now exposed.
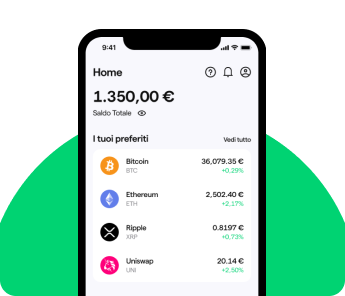
Young Platform takes strong security measures to ensure its reliability and does not ask its users for access credentials and other security codes.